Personal OPSEC Plan: Password Managers, FIDO Keys, and Email Protection

Online bettors, streamers, and affiliates handle cashflows, KYC documents, and account credentials that crooks love. A basic personal OPSEC plan stops most smash-and-grab attacks before they start. Whether you’re placing a weekend accumulator or managing an affiliate dashboard, treat your identity like a bankroll: protect it, track it, and never risk it all on a single point of failure. If you research mobile wagering, you’ll see a lot of chatter about best casino apps uk—great apps are convenient, but your own setup is the first and most reliable safety layer.
Phase 1 — Password Managers Done Right
Strong authentication starts with one habit: unique secrets for every account, stored in a vault you control. A password manager reduces friction while removing the two biggest causes of account takeovers: reuse and weak phrases. For gambling and iGaming work, that spans sportsbooks, wallets, affiliate panels, hosting, and email.
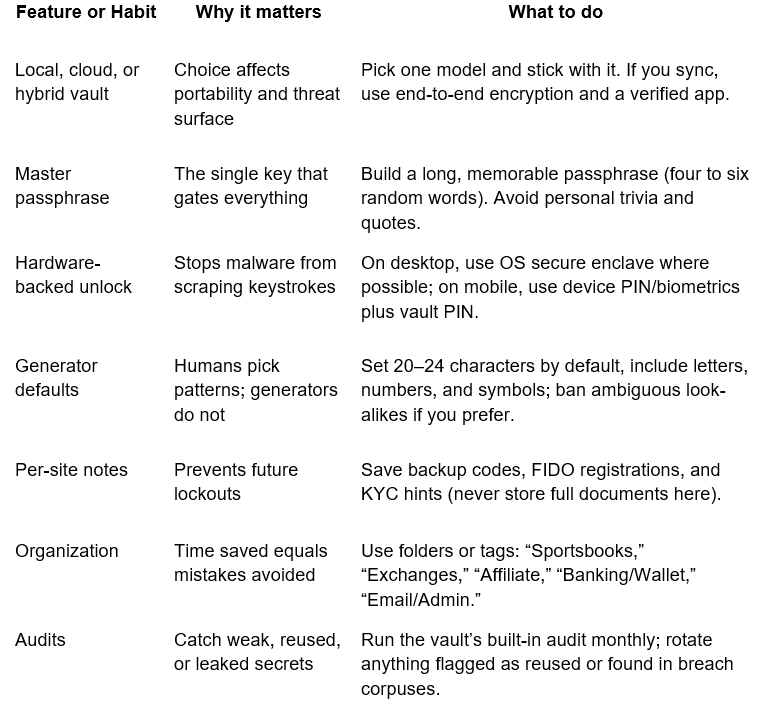
Takeaway: A password manager is your roster. Train it, keep it tidy, and keep substitutes ready (export + printed recovery kit in a safe place). Once the vault holds every credential, reuse stops by default and day-to-day friction drops fast.
Phase 2 — FIDO Keys and Email Protection (Aliases, DMARC, and Safer 2FA)
Once your vault is in shape, raise the bar for account entry and reduce the blast radius of any single inbox. FIDO2/WebAuthn hardware keys stop phishing by requiring cryptographic approval at the origin site; email controls and aliases help you separate risk across brands and campaigns.
- Rollout checklist for FIDO keys and email safety
-
Buy two FIDO2 keys: one primary on your keychain and one spare in a safe location. Register both anywhere that supports WebAuthn.
-
Prioritize high-value targets: email accounts, cloud storage, payment wallets, domain registrar, sportsbook apps, and affiliate panels. Add keys before enabling lesser forms of 2FA.
-
Keep an emergency path: store printed one-time backup codes in a fireproof bag; never store codes in the same vault that protects your logins.
-
Set phishing-resistant 2FA where possible: FIDO first. If a site only offers TOTP apps, use that. Avoid SMS codes for sensitive services; SIM swaps remain common.
-
Harden your primary inbox: turn on SPF/DKIM/DMARC for any domain you own (prevents fraud in your name). At providers that manage DNS, these take minutes to publish.
-
Use aliases for blast-radius control: one alias per bookmaker, exchange, or affiliate program. If spam or a breach hits one alias, you spot it quickly and can retire just that address.
-
Enable “security-only” forwarding: route provider security alerts to a second inbox you check from a separate device, reducing the chance a single compromise blinds you.
-
Apply device hygiene: OS auto-updates on, browser up to date, extensions reviewed monthly. A clean device makes everything above harder to bypass.
-
Takeaway: With keys registered, phishing links hit a wall. With aliases and domain controls in place, a crook cannot weaponize your name or drain every account through one compromised inbox.
Why OPSEC matters in gambling and iGaming work
Wagering accounts often link cards, e-wallets, crypto, and loyalty balances. Affiliates connect ad platforms, trackers, and hosting. Attackers go where fast payouts live. That risk climbs during major sporting events, during bonus seasons, and whenever you publish content that exposes your brand footprint.
A sensible target model for a bettor, streamer, or affiliate looks like this:
-
You are more likely to face phishing than zero-days.
-
You are more likely to misplace a phone than lose a hardware key stored on a big keyring.
-
You are more likely to approve a fake login prompt when rushing to place a market bet than during quiet hours.
Build your habits around those truths: hardware prompts you must physically touch beat any popup; unique email aliases reveal patterns in spam; a vault removes mental math at the worst possible moment.
Practical deployment playbook (7-day sprint)
You don’t need a month. A one-week cadence works well, even while running campaigns.
Day 1: Choose a password manager, set a long master passphrase, and turn on vault sync (or decide on local only). Add your browsers and phones.
Day 2: Import or manually enter your top-value accounts (email, registrar, wallets, sportsbooks, affiliate logins). Rotate anything weak or reused to 20–24 characters.
Day 3: Purchase two FIDO keys. Register both on email, registrar, and cloud storage. Print backup codes for those services and store them safely.
Day 4: Add FIDO to wallets, sportsbooks, and exchanges that support WebAuthn. Where not supported, set TOTP and store the secret in your vault (never screenshots).
Day 5: For any domain you own, publish SPF, DKIM, and a DMARC policy. Start with p=quarantine and a report address; review reports weekly and move to p=reject once records look clean.
Day 6: Create per-service email aliases. Update logins so each brand or platform uses a unique address. Add rules that label incoming messages by alias, so suspicious mail stands out.
Day 7: Run the vault’s audit, remove stale browser extensions, turn on automatic OS/browser updates, and test your recovery: use the spare key and a backup code to sign in.
Common pitfalls to avoid (and easy fixes)
-
Relying on SMS for high-value accounts: request app-based codes or FIDO. If a provider only offers SMS, keep that number on a separate line not used for messaging apps.
-
Saving 2FA codes in screenshots: store secrets in the vault field designed for TOTP, or keep offline printouts.
-
One email for everything: aliases cost little or nothing and pay off the first time a list leaks.
-
Forgetting to lock down the registrar: a domain hijack can reroute email and hosting in minutes. That account deserves the toughest setup you have.
Policy for shared projects and teams
If you run a tipster brand, a content studio, or an affiliate network, take the same ideas and add light process:
-
Least-access sharing: give staff vault access only to what they need. Sub-vaults for “Content,” “Finance,” “Admin.”
-
Key policy: team members keep two FIDO keys; the team stores a third “break-glass” key in a safe with access logged.
-
Offboarding checklist: rotate shared secrets, revoke keys, and retire aliases linked to the departing member.
-
Quarterly rehearsal: simulate account recovery with the spare key and backup codes; fix anything that breaks while the pressure is low.
Final thought
OPSEC isn’t drama; it’s a habit. A vault that holds every credential, a pair of FIDO keys you can touch, and an inbox strategy that splits risk will stop the majority of smash-and-grab attacks that target bettors and creators. Put this plan in place once, rehearse recovery twice a year, and you’ll spend the rest of your time on lines, odds, and content—not on cleanup.
