Understanding OAuth and JWT: Key Differences and Usage
In the realm of web development, securing user data and managing authentication is crucial. Two widely used standards in this domain are OAuth and JSON Web Tokens (JWT). While they share some similarities, they serve distinct purposes in authentication and authorization. This article delves into these differences, outlines their advantages and disadvantages, and explains how they can be integrated effectively.
What Is OAuth?
OAuth, or Open Authorization, is an open standard that facilitates secure token-based authentication across public networks. It allows third-party applications, such as Facebook or Google, to access user account information without exposing sensitive login credentials. Essentially, OAuth acts as an intermediary that provides access tokens to authorized third-party services, enabling them to interact with user data securely. The process of requesting and receiving these tokens is known as the authorization flow.
What Is JWT?
JSON Web Tokens (JWT) are a standardized method for transmitting information between two parties, typically a client and a server. A JWT consists of a JSON object that carries the necessary information, known as claims. Each token is cryptographically signed, ensuring that the contents cannot be manipulated by unauthorized users.
Comparing OAuth and JWT
Though OAuth and JWT both pertain to authentication and authorization, they excel in different scenarios.
OAuth vs. JWT: Key Differences
|Differences | OAuth | JWT |
| --- | --- |--- |
|** Main Functionality** | is primarily for authorization, allowing users to grant third-party access to their resources. |focuses on authentication and transporting data securely.|
| Security |provides a secure method for managing authorization flows. |is lightweight and self-contained but must be implemented within a secure authentication framework to maintain its integrity. |
|Statefulness|is stateful, requiring a connection to an authorization server to manage token validation.|are stateless, meaning they do not rely on an external server for validation.|
|Usage Scenarios|is better suited for managing session state on the server.|is ideal for stateless applications.|
|oken Types|issues unique tokens for resource access, typically managed by the identity provider (IDP).|contains user claims.|
Pros and Cons
Advantages of OAuth:
- Broad Adoption: Popular services universally implement OAuth 2.0, facilitating easy integration.
- Rich Ecosystem: Numerous ready-to-use OAuth solutions are available, particularly from social networks.
- Security: OAuth is rigorously tested in various programming environments.
Disadvantages of OAuth:
- Complexity: The multiple OAuth flows can be daunting for beginners.
- Possible Overkill: Simpler applications may not require OAuth's complexity.
- Privacy Concerns: Users may worry about how much information the authentication server can access.
Advantages of JWT:
- Efficiency: JWTs allow for quick verification without database queries.
- Client-Side Storage: Tokens are stored on the client side, saving server resources.
- Strong Security: JWTs are signed and tamper-proof.
Disadvantages of JWT:
- Revocation Challenges: Inability to revoke tokens quickly can be problematic without additional systems.
- Risk of Compromise: If the signing key is exposed, attackers can forge valid tokens.
When to Use JWT vs. OAuth
Choosing between JWT and OAuth depends on your application's needs:
-
Use JWT: When you require a compact method for transmitting information between clients and servers, especially in stateless applications or APIs. JWT is ideal for scenarios where performance and efficient user authentication are key.
-
Use OAuth: When you need to let users grant third-party applications access to their resources without sharing their passwords. This is especially useful in web applications and when handling complex user permissions.
Integrating JWT with OAuth2
While JWT and OAuth2 are distinct, they complement each other well. The OAuth2 protocol does not prescribe a specific token format, making it possible to use JWTs for tokens issued by OAuth2 authorization servers. For instance, the access token generated could be a JWT containing critical payload information. This combination can enhance performance and reduce the need for frequent communication between servers.
Using OAuth and JWT with EchoAPI
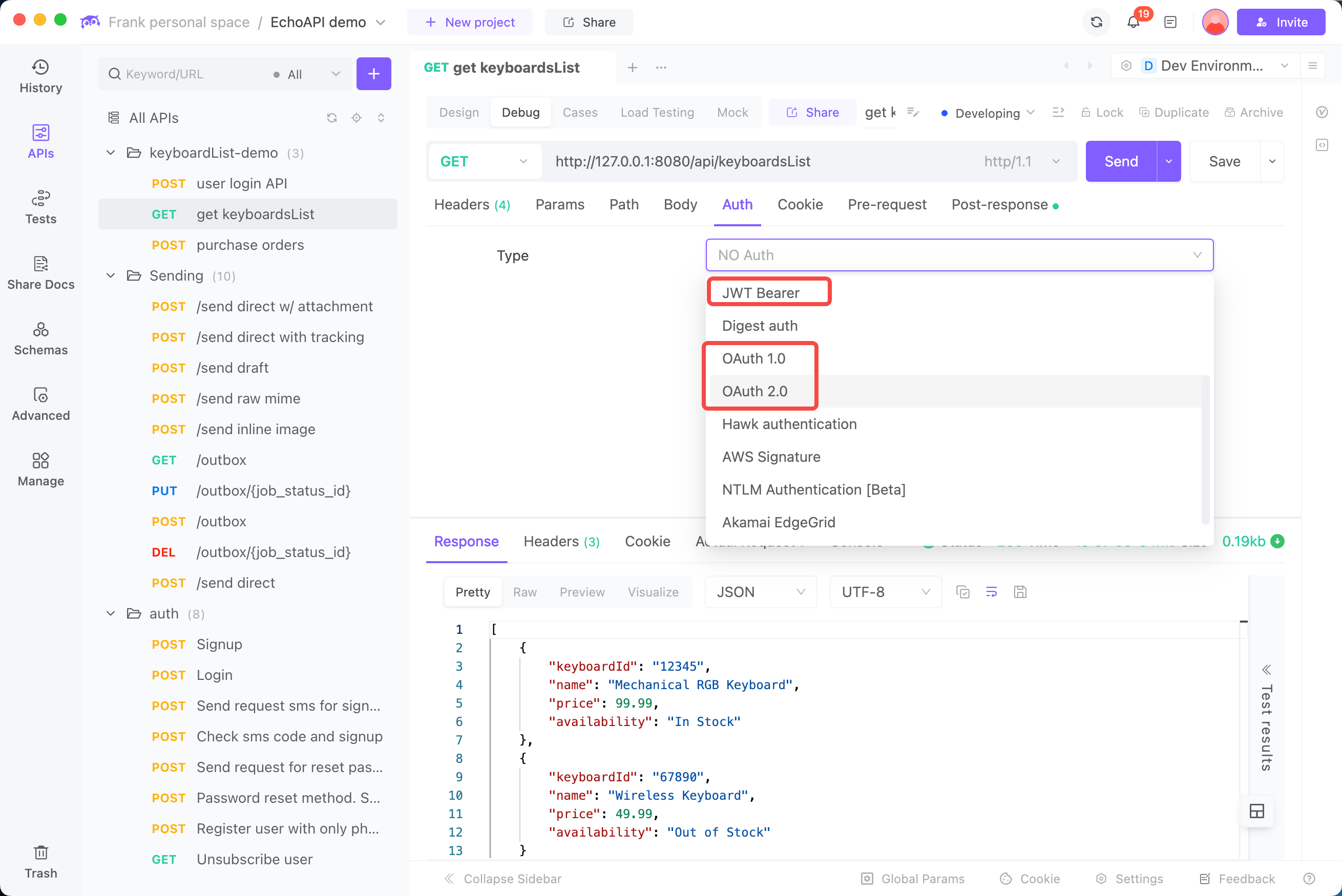
EchoAPI provides a comprehensive authentication infrastructure based on JSON Web Tokens, adhering to top security standards. EchoAPI ensures compatibility with the OAuth protocol and OpenID Connect, offering robust user management for modern SaaS applications.
Moreover, EchoAPI facilitates seamless integration with various third-party solutions, utilizing JSON Web Key Set (JWKS) endpoints, refresh tokens, and public certificates aligned with the JWT mechanism. This feature enhances development efficiency and enables swift deployment of JWT-secured applications.
In conclusion, leveraging OAuth and JWT together can fortify your application's security while simplifying authentication processes. With the right approach, you can harness the power of both to enhance user experience and protect sensitive data.
